
The Hollywood Hacker
If you got into cybersecurity because of Mr. Robot, you’re not alone. That show did something no certification course ever could. It made people feel what it might be like to actually understand how systems work, and to use that understanding in ways that most people could never imagine. For me it was a different piece of cinema, Hackers. Through its campy style and laughable “this is hacking” graphics I felt compelled to join the computer counter culture. It made the idea of being a hacker feel genuinely exciting.
The reality is different from the screen, obviously. It’s more methodical, more frustrating, and significantly less dramatic. But the thing that draws people in is real. The idea of pushing a system to do something its creator didn’t intend, the freedom of finding a path that wasn’t supposed to exist. For many of us, that’s the reason we chose this field. So did I end up falling down the rabbit hole and start exploring the darker side of computer networking? Not exactly.
I came at this from a different angle. Yes, I wanted to explore what being a hacker was really all about, but I was also inspired by telling my own stories. So I made the jump, moved to L.A., and spent fifteen years working in film and television before making my move into cybersecurity. I was in the trenches of broadcast production, the windowless editing rooms, cutting features and producing reality TV. The kind of content that shapes what people think the world looks like. And just like real world cybersecurity work doesn’t look like Hackers, real world production doesn’t look like Entourage. When I eventually made the move into security, I found something I didn’t expect: the skills that had made me good at my old job were some of the most useful things I brought with me.
The Part Nobody Shows You in the Montage

In every hacking movie, there’s a scene where someone sits down at a keyboard and within thirty seconds they’ve cracked the mainframe, bypassed the firewall, and delivers my favorite line: “I’m in.”
What actually happens when you’re starting out in pentesting is closer to this: you run a tool, you get back several hundred lines of output, and you stare at it trying to figure out what any of it means, then spend more time than you’d like to admit reading the man page. Sure, there are some wizards out there who make it look easy, but that’s not me. Not yet.
Take nmap, the port scanner that most people learn first. The great joke of r/masterhacker. A basic scan of a target can return dozens of open ports, service versions, operating system guesses, and script output, all at once. When you’re new, it looks like noise. It looks like hacking. You’re not sure what’s important, what’s irrelevant, and what’s the thread you’re supposed to pull.
That feeling, being buried in information and not knowing where to start, is one of the most common experiences for people early in their pentesting journey. And it doesn’t fully go away as you get more experienced. The environments just get larger and the data gets denser.
What the Job Actually Was

A story producer on a reality television show has one core problem: you have hundreds of hours of footage and you need to find the story inside it.
Not a story. The story. The one that matters. The one with a beginning and an end that an audience will actually follow. You have to connect the A-story to the B-story and make sure your thematic message tracks. Everything else, the filler, the tangents, the moments that don’t connect to anything, gets left on the cutting room floor.
As an editor, you do the same work at a more granular level. You have a sequence of moments and you’re constantly asking: what order do these go in? What does the audience need to understand before this next thing lands? What’s the shortest path from confusion to clarity?

What I didn’t realize until I was deeper into learning pentesting was that this was exactly the skill I needed. The job of a penetration tester, at least the thinking part of it, is finding the path through an enormous amount of information that might lead somewhere useful. Just like finding the story, you’re often cut off by dead ends and useless rabbit holes. But slowly, as you run your tools and dig a little deeper, you build a picture, piece by piece, of how a system fits together and where the gaps are.
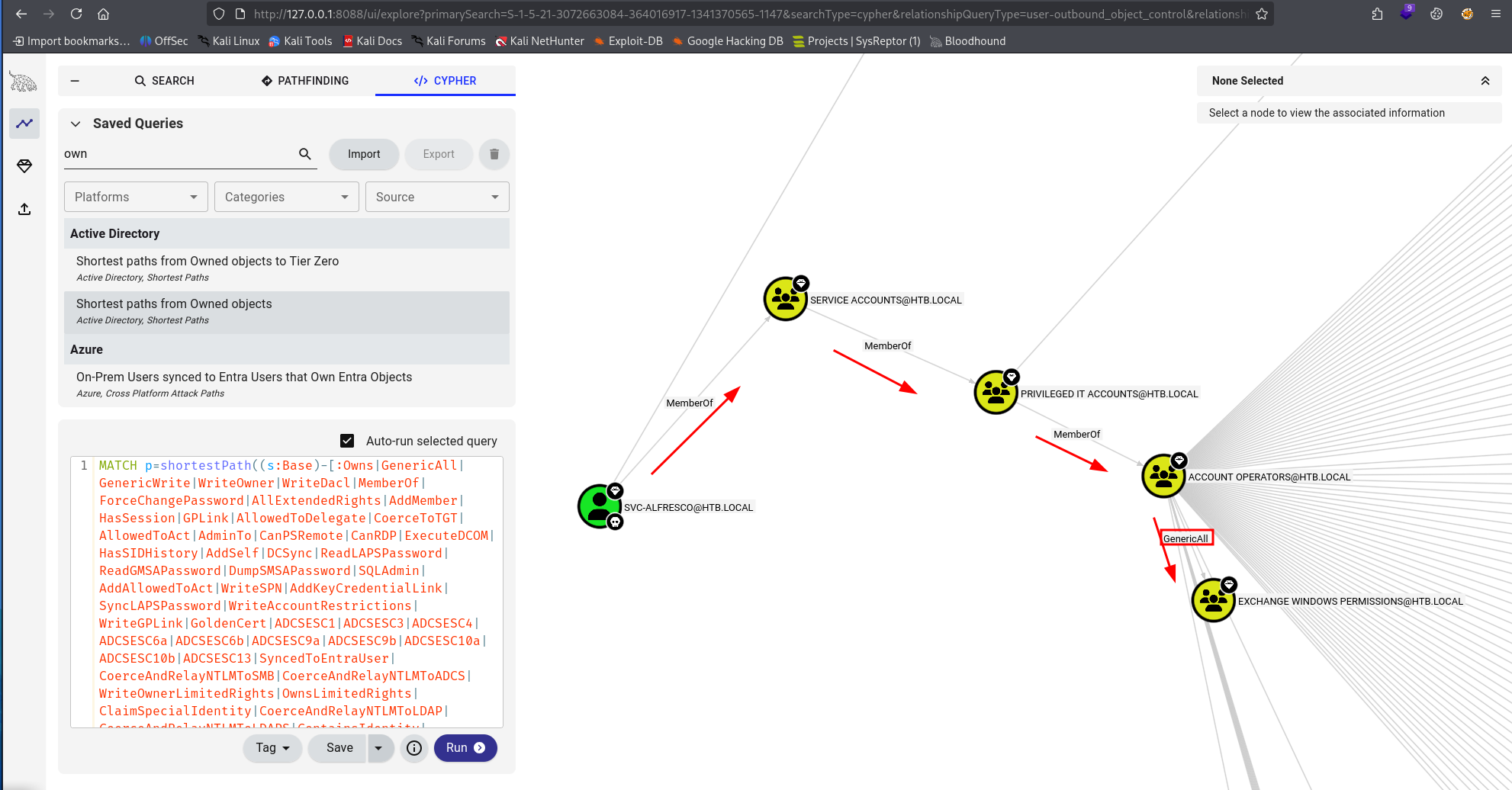
When I first opened BloodHound and saw a rendered graph of an Active Directory environment with hundreds of nodes, thousands of edges, relationships between users and groups and computers sprawling across the screen, I was overwhelmed. Then my instinct kicked in and I thought: this is just footage. And I already knew how to find the story in footage.
Staying Calm When Everything Is Loud

Television production is not a relaxed environment. There are always too many things happening at once, the deadline is always real, and the consequences of missing it are visible and immediate. If you ever get the chance to walk onto a set in production, between takes, it is a chaos of movement and action. You can easily spot the newbies from the old pros. The newbies are the ones standing still, unsure of what they should be doing, overwhelmed by the chaos.
You learn something from years of being exposed to it, something that is genuinely hard to learn any other way: how to keep your head clear when everything around you is stressful and chaotic. People are yelling for something to be done now, and there is no way it will happen. Eventually you learn how to continue making good decisions when the pressure is high, the information is incomplete, and someone with more authority than you is demanding an answer.
If you’re studying for the CPTS or working through harder Hack The Box machines, you’ve probably already had a taste of this. You’re two days into a problem, you’ve tried fifteen things, nothing has worked, and the temptation to either give up or start running tools randomly is very real. Sure, the walkthroughs exist and are part of the teaching process, but there is no walkthrough for the exam or for real life. The people who push through that moment and come out the other side with a working approach are building the mindset needed for this work.
I built that on multi-million dollar productions where screwups cost jobs and more money than you want to even think about. It’s a trial by fire that everyone faces eventually, but you can get ahead of the curve by practicing in the labs. The mechanism is different but the result is the same. Stay calm, have a process, a methodology. Work from principles rather than if/then thinking. Move forward with a clear vision in mind, but expect and embrace the changes that come up.
Communication Is the Other Half of the Job
Here’s something Mr. Robot gets right that most people don’t think about: Elliot’s real power isn’t that he can hack things. It’s that he understands people well enough to know what to say, when to say it, and who needs to hear it. The social engineering angle is closer to the actual job than the keyboard montages.

In real pentesting, you will eventually have to explain what you found to someone who didn’t do the work with you. That might be a technical lead who wants the details. It might be an executive who wants to know the business impact in three sentences. It might be a client who is defensive about findings on their infrastructure and needs to be handled carefully.
Writing a clear finding, one that explains what the vulnerability is, what an attacker could do with it, and what needs to change, is not a skill that comes automatically from being technically good. It’s a different skill. And it matters, because a finding that doesn’t communicate clearly is a finding that doesn’t get fixed. You know what’s important to you, but you have to phrase your findings in a way that’s important to the one listening.
Fifteen years of explaining complicated situations to people who weren’t in the room gave me a running start on that. But it’s something anyone can develop deliberately, and I’d argue it’s worth as much as any technical certification if you want to actually work in this field.
What This Means If You’re Just Starting Out
If you’re early in your security journey, working through HTB, grinding certs, watching Mr. Robot for the third time and wondering if you’re cut out for this, here’s what I’d tell you.
The technical skills are learnable. The curriculum exists. The labs exist. If you put the hours in, the technical knowledge will come. The mindset is something that is discovered, something that is chosen.
What will separate you from other people at a similar technical level is the non-obvious stuff: the ability to stay calm and keep thinking when you’re stuck, to communicate what you found in a way that’s actually useful, to find the signal in a wall of output.
Those skills don’t always come from technical study. They come from being in situations that require them, in labs, in CTFs, in real engagements, or as it turns out, on Hollywood film sets.
The path I took to get here will be different than the path that brought you here. But every path has its skills that are essential to getting the work done and helping you excel. It’s worth figuring out what those things are and making sure they aren’t lost in the sea of certs and boxes.